Editorial Policies
Contents
- Ethical Standards and Principles
- Advertising Policy
- Affiliations
- Appeals and Complaints
- Acknowledgment Policy
- Authorship
- Citations
- Conflicts of Interest / Competing Interests
- Corrections, Expressions of Concern, and Retractions
- Consent for Publication
- Confidentiality Policy
- Copyright, Licensing, and Access
- Data Fabrication and Falsification
- Data Sharing Policy
- Desk Rejection Policy
- Duplicate Submission and Publication
- Funding
- Images and Figures
- Research and Publication Misconduct
- Peer Review
- Publication Ethics
- Plagiarism Policy
- Preprints Policy
- Protection of Participants’ Privacy
- Special Issues Policy
- Standards of Reporting
- Use of Third-Party Material
- Use of Generative AI and AI-Assisted Technologies in Writing
Ethical Standards and Principles
The Mesopotamian Journal of CyberSecurity (MJCS) is a follower of the Committee on Publication Ethics (COPE) guidelines.
Submission of a manuscript to MJCS implies that all authors have read and agreed to its content, that the manuscript conforms to the journal’s ethical and editorial policies, and that it has not been published or is under consideration elsewhere. The journal upholds integrity, transparency, and accountability at every stage of the editorial and publishing process.
Advertising Policy
The Mesopotamian Journal of CyberSecurity maintains strict ethical standards to preserve its editorial independence and scholarly integrity.
The journal does not accept advertisements from third parties in any form, whether print or digital.
This policy ensures that editorial decisions remain entirely independent of any commercial influence and that all published content reflects the journal’s commitment to scientific integrity and objectivity.
Affiliations
- Authors must provide accurate and complete institutional affiliations to properly attribute where the research was approved, supported, or conducted.
- For non-research articles, the author’s current institutional affiliation must be listed.
- If an author has moved to another institution prior to publication, they should list both the institution where the work was conducted and their current affiliation in the acknowledgment section.
- Misrepresentation of affiliation is considered a form of publication misconduct, and any such cases will be investigated in accordance with COPE procedures.
Appeals and Complaints
The Mesopotamian Journal of CyberSecurity follows the COPE guidelines on handling appeals, complaints, and editorial disputes.
Authors may submit a formal appeal to the Editors-in-Chief if they believe that an editorial decision was based on a misunderstanding or procedural error. Appeals must include clear justification and supporting evidence addressing the reviewers’ or editors’ comments.
All complaints related to authorship, peer review, or editorial management will be investigated objectively by the Editors-in-Chief or designated senior editors. If a complaint involves an editor directly, the Editorial Board—led by the most senior member—will independently review the matter and propose corrective action consistent with ethical best practices.
Acknowledgment Policy
Individuals who have contributed to the research or manuscript but do not meet authorship criteria should be recognized in the Acknowledgments section. This may include individuals who provided technical assistance, data collection, administrative support, language editing, or critical discussion of the manuscript.
Authors are responsible for obtaining written permission from any individuals they wish to acknowledge.
Groups that contributed materially to the work (e.g., research teams, lab technicians, or advisory committees) may be listed collectively with their specific role described (e.g., “provided data analysis,” “assisted in fieldwork,” etc.).
If any AI tools or automated content generators (e.g., ChatGPT or similar systems) were used during manuscript preparation, this must be clearly disclosed in the Acknowledgments, specifying the scope of their use. Authors remain fully accountable for the accuracy, originality, and integrity of all manuscript content.
Authorship
Listing authors on an article credits those who made substantial scholarly contributions and ensures accountability for the integrity of the work. All listed authors must meet all of the following criteria:
- Substantial contribution to the work reported (e.g., conception; study design; execution; acquisition, analysis, or interpretation of data).
- Writing or critical revision of the article for important intellectual content.
- Agreement on the journal of submission and on the order of authors.
- Approval of all versions of the manuscript (at initial submission, during revision, at acceptance, and at proof) and of any substantive post-acceptance changes.
- Accountability for the accuracy and integrity of the work and willingness to resolve questions related to it.
Authorship changes
Any addition, removal, or re-ordering of authors before or after publication must be approved by all authors (including those added/removed). The corresponding author must provide (i) a clear reason for the change and (ii) written confirmation from every author. Requests after acceptance are granted at the Editors-in-Chief’s discretion and, if approved post-publication, will be documented via a formal notice.
Affiliations
If an author’s affiliation changes between research and publication, list the affiliation where the work was conducted and note the current affiliation (e.g., in Acknowledgments). Misrepresentation of affiliation is considered misconduct.
Contribution transparency (CRediT)
All articles submitted from 2026 onward must include a contribution statement using the CRediT taxonomy (e.g., Conceptualization, Methodology, Software, Validation, Formal analysis, Investigation, Resources, Data curation, Writing–original draft, Writing–review & editing, Visualization, Supervision, Project administration, Funding acquisition).
What does not justify authorship
Funding acquisition alone, general supervision, routine data collection, or minor editing do not qualify; such contributions should be acknowledged.
Citations
Submissions must cite relevant, timely, and verifiable literature (peer-reviewed where appropriate) to substantiate claims and situate the work within the scholarly record.
- Avoid citation manipulation. Excessive self-citation, coordinated cross-citation (“citation cartels”), or coercive citation is prohibited and may lead to rejection or correction.
- Balance. Reviews and perspectives must present a fair, unbiased overview of current research; references should not be unduly concentrated on a single group, organization, or journal.
- Uncertain sources. If in doubt about citing a source or grey literature, contact the editorial office before submission.
Conflicts of Interest / Competing Interests
All authors must disclose financial and non-financial interests that are relevant to—or could reasonably be perceived to influence—the submitted work. Declarations appear before references section in the article.
Examples of potential conflicts include (not exhaustive):
- Financial: employment, consultancies, honoraria, royalties, paid expert testimony, patents (planned/issued/licensed), stock/stock options, grants or in-kind support.
- Non-financial: leadership roles, advisory board memberships, advocacy group collaborations, access to privileged data or materials, personal/ideological/academic relationships, or ongoing legal actions related to the work.
If no conflicts exist, the article will state: “The authors declare no competing interests.” Editors and reviewers must also recuse themselves from handling manuscripts where conflicts exist.
Industry-sponsored work. Authors employed by or funded by organizations (including cybersecurity vendors) must declare this support and follow COPE guidance.
Corrections, Expressions of Concern, and Retractions
MJCS maintains the integrity of the scholarly record in accordance with COPE guidance.
- Corrections (Errata/Corrigenda). Issued when an error affects the understanding, indexing, or reliability of the article but does not invalidate its conclusions. Publisher-introduced errors are labeled Erratum; author-introduced errors are Corrigendum.
- Expressions of Concern. May be issued when substantial concerns arise (e.g., serious methodological or ethical issues) but an investigation is inconclusive or will require extended time.
- Retractions. Issued when conclusions are invalid or when serious misconduct is confirmed (e.g., plagiarism, duplicate publication, image/data manipulation, lack of required approvals). Retractions link bidirectionally to the original article; the HTML/PDF are watermarked “Retracted,” and a clear reason and the requesting party are stated.
- Removals. In rare legal or safety circumstances (e.g., defamation, court orders), an article may be removed and replaced with a Removal Notice.
All post-publication notices are permanent, citable, and linked to the version of record. Authorship disputes are usually handled via correction rather than retraction.
Consent for Publication
For all manuscripts that include personal data, identifiable details, or images relating to individuals, written informed consent for publication must be obtained from those individuals (or from their parent/legal guardian in the case of minors under 18). Consent must cover publication under the Creative Commons Attribution License (CC BY 4.0), which allows free distribution and public accessibility on the internet.
If the individual has passed away, consent should be obtained from their next of kin. Manuscripts must include a statement confirming that written informed consent has been obtained.
Authors may use the MJCS consent form or an equivalent institutional/ethical consent form that complies with local regulations. The consent must clearly state that the information will be freely available online and may be seen by the general public. Copies of consent documentation must be made available to the Editor upon request and will be treated confidentially.
Confidentiality Policy
All submissions to the Mesopotamian Journal of CyberSecurity (MJCS) are treated as confidential materials. Manuscripts are not disclosed to anyone outside of those directly involved in the review and publication process — including editorial staff, editors, and peer reviewers.
MJCS strictly adheres to COPE guidelines and relevant data protection laws, including the General Data Protection Regulation (GDPR). During peer review, reviewers must not share, copy, or discuss manuscripts with anyone without prior permission from the Editor. If a reviewer wishes to involve a colleague as a co-reviewer, prior editorial approval must be obtained, and full disclosure of the co-reviewer’s identity and potential conflicts of interest must be provided.
In cases involving ethical or publication misconduct, the journal may share information with the relevant institutional ethics committees or authorities to ensure a fair investigation and resolution. All parties involved — including whistleblowers — will be treated in confidence.
Copyright, Licensing, and Access
Copyright Policy
The Mesopotamian Journal of CyberSecurity (MJCS) publishes all content under the Creative Commons Attribution (CC BY 4.0) License. This license allows others to share, adapt, and distribute the published material in any medium or format, provided that appropriate credit is given to the original author(s) and the journal.
Authors retain full copyright of their work, while granting MJCS and its publisher, Mesopotamian Academic Press (MAP), the right to publish and disseminate the article. By submitting a manuscript, authors confirm that their work is original, has not been published elsewhere, and does not infringe on any third-party rights. Re-use of published material must always include a citation to the original article and the statement of the CC BY 4.0 license.
Who Can Submit?
Anyone may submit an original manuscript for consideration in the Mesopotamian Journal of CyberSecurity (MJCS), provided they own the copyright to the work or are authorized by the copyright holder(s) to submit it. Authors are the initial copyright owners of their manuscripts prior to publication, except in cases where an employment contract transfers ownership to an employer or funding institution.
By submitting to MJCS, authors confirm that their manuscript is original, has not been published elsewhere, and is not under review by any other journal or publisher.
User Rights
The Mesopotamian Journal of CyberSecurity (MJCS) is an open-access publication. All users have the right to read, download, copy, distribute, print, search, or link to the full text of articles published in MJCS, provided appropriate credit is given to the authors and the journal.
All articles are published under the terms of the Creative Commons Attribution License (CC BY 4.0), which permits unrestricted reuse, distribution, and reproduction in any medium, as long as the original author(s) and source are properly credited.
A license logo is embedded within every published article.
Open Access Policy
The Mesopotamian Journal of CyberSecurity (MJCS) operates under a Gold Open Access model, providing immediate and permanent free access to all published content. All peer-reviewed research articles are made freely accessible online at the time of publication, ensuring that the journal’s content is available to researchers, practitioners, and the general public worldwide without subscription barriers.
All articles in MJCS are published under the Creative Commons Attribution License (CC BY 4.0), which allows others to copy, distribute, transmit, and adapt the work, including for commercial purposes, provided the original work is properly cited.
Authors retain full copyright and grant the journal the right to publish their work and make it publicly available. This license promotes the widest possible dissemination and reuse of academic knowledge while preserving authorship recognition.
Information on the Article Processing Charge (APC) is available on the Author Guidelines page.
Author Rights
The Mesopotamian Journal of CyberSecurity (MJCS) allows authors to retain copyright of their work while granting the journal and its publisher, Mesopotamian Academic Press (MAP), a non-exclusive license to publish, distribute, and promote the article.
Authors therefore:
- Retain full copyright and scholarly usage rights.
- Are free to share, deposit, and reuse their published work, provided that proper attribution to the original publication in MJCS is given.
- May include their article in institutional repositories, personal websites, or future works, provided that the original citation and DOI are included.
This policy ensures that authors maintain control over their intellectual property while enabling the widest possible dissemination of their research.
Data Fabrication and Falsification
The MJCS maintains zero tolerance toward data fabrication, falsification, or manipulation. Deliberate alteration or misrepresentation of data constitutes serious research misconduct and undermines the credibility of the scientific record.
Authors submitting manuscripts must ensure that:
- All data accurately reflect the research conducted.
- Figures, tables, and images are original and not manipulated in ways that could mislead readers.
- Original/raw data corresponding to the study are retained and available for verification upon request by editors or reviewers.
If the underlying data cannot be provided upon request, or if evidence of fabrication or manipulation is found, the manuscript may be rejected or a published article retracted in accordance with COPE guidelines.
Data Sharing Policy
The Mesopotamian Journal of CyberSecurity encourages responsible sharing of research data to promote transparency, reproducibility, and advancement of cybersecurity knowledge.
Our data-sharing principles include:
- Encouraging authors to share research data early, where appropriate, through trusted repositories.
- Promoting the inclusion of Data Availability Statements in all submissions starting from 2026 to clarify where and how supporting data can be accessed.
- Supporting proper data citation practices, ensuring authors receive credit for shared data.
- Collaborating with institutions and the cybersecurity research community to develop robust data validation and review practices.
- Supporting data as an independent, peer-reviewed scholarly output when feasible.
Data Availability Statement Examples:
- Data available in a public repository:
“The datasets generated and/or analyzed during this study are available in the [Repository Name] at [Persistent Link].” - Data available upon request:
“The data supporting the findings of this study are available from the corresponding author upon reasonable request.” - No data available:
“No datasets were generated or analyzed during the current study.”
Authors should ensure that any data sharing complies with ethical, legal, and institutional requirements (e.g., privacy, security, and classified information considerations).
Desk Rejection Policy
Submissions to the Mesopotamian Journal of CyberSecurity (MJCS) are evaluated first for scope, quality, and compliance with publication standards. A manuscript may receive an immediate desk rejection without external peer review if it meets any of the following criteria:
- The topic or scope of the study does not align with the journal’s field or aims.
- The manuscript exhibits ethical or plagiarism issues, or non-adherence to international publication guidelines.
- The study lacks sufficient originality, novelty, or contribution to cybersecurity knowledge.
- The research design or methodology is flawed or incomplete.
- The study’s objectives are unclear or poorly articulated.
- The organization or presentation of the manuscript is problematic, or sections are missing.
- The writing contains serious grammatical or stylistic issues that impede clarity.
- The submission does not follow the MJCS author guidelines or formatting requirements.
Desk rejection allows editors to ensure that only manuscripts meeting scientific, ethical, and editorial standards proceed to peer review.
Duplicate Submission and Publication
Authors must confirm at submission that their manuscript is not under consideration elsewhere and has not been published previously, in any language or format. Submitting or publishing the same content in multiple journals constitutes duplicate publication, which is a form of ethical misconduct.
- For secondary publications (e.g., translations), authors must obtain written permission from the original publisher and clearly cite the original article.
- The translated article must identify itself as such and include full acknowledgment of the primary publication.
- Manuscripts discovered to be duplicated will be withdrawn or retracted, and appropriate actions will be taken against the submitting authors.
Funding
For all submissions from 2026 onward, authors must declare all sources of financial or institutional support for their research within the manuscript. This includes grants, fellowships, institutional funding, and commercial or governmental sponsorships. The declaration should specify the role of the funder(s) in study design, data collection, analysis, and publication decisions—or explicitly state that the funder had no involvement. Transparency regarding funding ensures compliance with institutional and sponsor requirements and helps maintain research integrity.
Images and Figures
Authors should include images, figures, or graphics only when they contribute meaningfully to the research. Purely decorative or illustrative content that does not enhance the scholarly work should be avoided.
- Any third-party material (text, figures, tables, graphics, video, etc.) must be accompanied by written permission from the copyright holder before inclusion.
- Photographs, video, or audio recordings that could identify individuals require informed Consent to Publish (from the subject, parent/guardian, or next of kin, as appropriate).
- Authors must adhere to ethical and cultural norms regarding sensitive material, including images of human remains or identifiable persons.
- Scientific integrity of images:
- Images (e.g., microscopy, system diagrams, screenshots) must represent data accurately and must not be manipulated in a way that alters interpretation.
- Any digital enhancement (contrast, brightness, color correction) must be applied uniformly and described in the figure legend.
- Grouping of images (e.g., gels or blots) must be explicitly stated.
- Authors must be prepared to submit original, unprocessed images upon editorial request.
- Re-use of previously published figures requires documented copyright permission and citation of the original source.
Failure to comply with these image integrity standards may result in rejection or post-publication correction/retraction.
Research and Publication Misconduct
The Mesopotamian Journal of CyberSecurity takes all forms of misconduct seriously and follows the procedures outlined by Committee on Publication Ethics (COPE) to safeguard the integrity of the scholarly record.
Examples of Misconduct Include:
- Plagiarism or text recycling (self-plagiarism).
- Duplicate or redundant submission/publication.
- Data or image manipulation/fabrication.
- Misrepresentation of affiliation or authorship.
- Citation manipulation or coercive citation practices.
- Undisclosed conflicts of interest or funding sources.
- Unethical research practices (“ethics dumping”).
- Peer-review manipulation or falsification.
- Breaches of copyright or re-use without permission.
All allegations of misconduct will be investigated confidentially according to COPE flowcharts. Confirmed violations may result in rejection, retraction, author notification to affiliated institutions, and publication of formal notices (e.g., correction, expression of concern, or retraction).
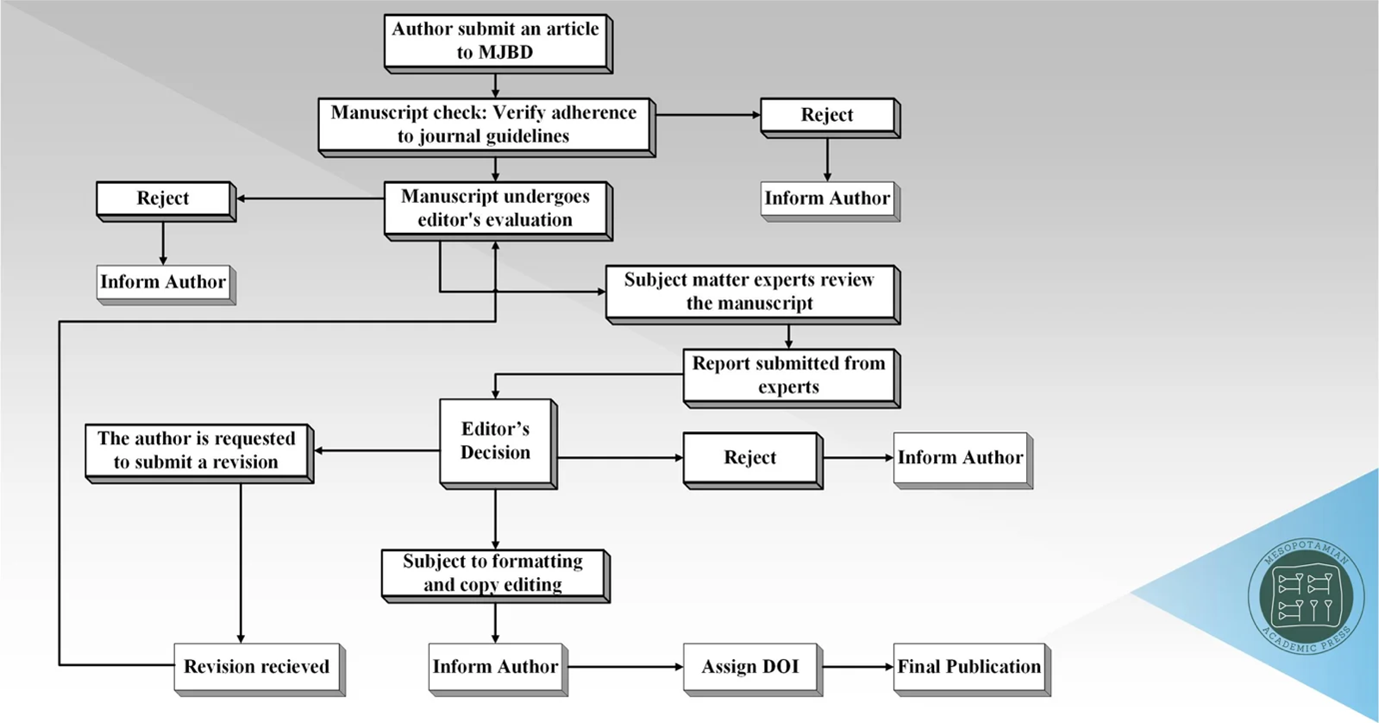
Peer Review
All manuscripts submitted to the journal undergo a rigorous double-blind peer-review process, in which the identities of both authors and reviewers are kept strictly confidential to ensure impartiality, fairness, and academic integrity.
- Initial Editorial Screening
Upon submission, each manuscript is first evaluated by the Editorial Office to verify compliance with the journal’s aims and scope, formatting requirements, ethical standards, and basic methodological soundness. Submissions may be desk-rejected at this stage if they are clearly outside the journal’s scope, fail to meet ethical requirements, or demonstrate fundamental scientific deficiencies.
- Assignment to Handling Editor
Manuscripts that pass the initial screening are assigned to a Handling Editor with relevant subject-matter expertise. The Handling Editor oversees the peer-review process and ensures that it is conducted in accordance with journal policies and international best practices.
- Reviewer Selection and Invitation
The Handling Editor invites at least two independent expert reviewers who possess appropriate academic or professional expertise in the manuscript’s subject area. Reviewers are selected based on scholarly competence, publication record, and absence of conflicts of interest. Reviewer anonymity is preserved throughout the process.
- Double-Blind Peer Review
Reviewers evaluate the manuscript based on clearly defined criteria, including but not limited to:
- Originality and contribution to the field,
- Methodological rigor and validity,
- Clarity of presentation and logical coherence,
- Appropriateness of data analysis and interpretation, and
- Relevance to the journal’s readership.
Reviewers provide detailed, constructive reports and make one of the following recommendations:
- Accept without revision
- Minor revision
- Major revision
- Reject
- Editorial Decision
The Editorial Board considers all reviewer reports and makes a decision based on their recommendations, the quality of the manuscript, and its alignment with the journal’s standards. In cases of conflicting reviews, additional reviewers may be consulted to ensure a balanced and fair assessment.
- Revisions and Re-Review (if applicable)
Authors receiving revision requests are expected to address all reviewer comments in a clear, point-by-point response. Revised manuscripts may be returned to the original reviewers for further evaluation, particularly in cases of major revision.
- Ethical, Security, and Societal Oversight
For manuscripts involving ethical concerns, security-sensitive content, biosecurity issues, artificial intelligence risks, or broader societal implications, the editors may seek additional specialist or ethics committee advice before reaching a final decision.
- Final Decision and Acceptance
Once all review requirements are satisfactorily met, the Editor-in-Chief or delegated senior editor issues the final acceptance decision. Accepted manuscripts proceed to copyediting, proofreading, and publication.
Publication Ethics
Duties of Editors
- Publication Decisions: The editorial board is responsible for deciding which manuscripts are suitable for publication based on scholarly merit, originality, relevance, and ethical compliance. Decisions are guided by the journal’s policies, reviewers’ recommendations, and applicable legal requirements concerning libel, copyright, and plagiarism. Editorial decisions are made impartially and are not influenced by an author’s nationality, ethnicity, gender, institutional affiliation, or political or religious beliefs.
- Confidentiality, Disclosure, and Conflicts of Interest: Editors must maintain strict confidentiality regarding all submitted manuscripts and may not disclose information to anyone outside the review process except the corresponding author, reviewers, or editorial advisers. Unpublished material must not be used in editors’ or reviewers’ own research without explicit written consent from the author. Editors must also disclose any potential conflicts of interest and ensure transparency regarding funding sources and the role of funders in the research or publication process.
- Author Relations: Editors ensure that the peer review process is fair, unbiased, and timely. Submissions from editorial board members are handled independently to avoid conflicts of interest. Clear author instructions are provided to ensure that all contributors meet authorship criteria.
- Reviewer Relations: The editorial team encourages reviewers to identify ethical issues (e.g., data manipulation, plagiarism, duplicate submission) and to provide constructive, evidence-based feedback. Reviewers’ identities remain confidential. Editors ensure reviewers’ contributions are recognized and discontinue engagement with reviewers who consistently provide poor-quality or disrespectful feedback.
- Quality Assurance: Editors take all reasonable steps to maintain the scientific and editorial quality of published material. They verify that submitted research has received appropriate ethical approvals (e.g., institutional review boards) and ensure that errors, misleading data, or ethical concerns are corrected promptly through retraction, correction, or erratum notices when required.
Duties of Reviewers
- Contribution to Editorial Decisions: Peer reviewers assist editors by evaluating the academic quality, originality, and rigor of manuscripts. Reviews must be objective and supported by clear arguments that authors can use to improve their work. Personal criticism is strictly prohibited.
- Qualifications and Conflicts of Interest: Reviewers should accept assignments only within their areas of expertise and must decline if they cannot complete the review on time or have conflicts of interest (e.g., collaborative, financial, or competitive relationships with authors or institutions).
- Confidentiality: All manuscripts and associated materials received for review must be treated as confidential documents and must not be shared or discussed with others. Privileged information obtained through peer review must not be used for personal advantage.
- Acknowledgment of Sources: Reviewers should identify relevant work not cited by authors and notify the editor of any suspected plagiarism, duplication, or significant overlap with other published material.
Duties of Authors
- Reporting Standards: Authors must present an accurate and objective account of their research and its significance. Data should be represented faithfully, and sufficient detail should be provided to allow replication. Fabrication, falsification, or misrepresentation of data is unethical and unacceptable.
- Originality and Plagiarism: Authors must ensure their work is entirely original. All references, quotations, and reused content (text, data, or images) must be properly cited. Simultaneous submission to more than one journal or redundant publication is strictly prohibited. All manuscripts are screened using professional plagiarism detection software; those with unacceptable similarity levels are rejected immediately.
- Disclosure and Conflicts of Interest: Authors must disclose all financial or non-financial conflicts of interest that could influence their results or interpretation, as well as all funding sources supporting the research.
- Authorship of the Paper: All individuals who have made a significant contribution to the conception, design, execution, or interpretation of the study must be listed as authors. The corresponding author ensures that all co-authors have approved the final version of the manuscript and consented to its submission.
- Fundamental Errors: If an author discovers a significant error or inaccuracy after publication, they must promptly notify the editor and cooperate in issuing a correction or retraction.
Plagiarism Policy
Authors are advised to observe high standards in publication ethics. MJCS strictly prohibits practices such as plagiarism, fabrication, and falsification of data, as well as duplicate publication without proper citation.
In line with our commitment to upholding publication ethics, we have implemented a comprehensive policy to address the issue of high AI plagiarism. Starting from May 1st, 2023, which coincides with the launch of Turnitin's AI detection capability, all manuscripts submitted for publication will be subjected to a thorough plagiarism check using Turnitin. This check will take place after submission and before the manuscripts are sent to the editor for editorial review.
Should any overlapping or similar texts be detected in the submitted manuscripts, our journal will promptly initiate an investigation. Manuscripts found to have a significant level of AI plagiarism will be considered unacceptable and may result in rejection.
By implementing this policy, we aim to ensure the originality and integrity of the research published in MJCS. We encourage authors to uphold the principles of academic integrity and contribute to the advancement of knowledge in an ethical and responsible manner.
Preprints Policy
Authors may post and share their preprints (e.g., on arXiv, SSRN, or institutional repositories) at any stage, provided that they clearly acknowledge the preprint version and link to the final published version using its DOI after acceptance. Posting a preprint is not considered prior publication.
Protection of Participants’ Privacy
Patient or participant identity must never be disclosed unless explicit written consent has been obtained. Authors must remove identifying details (names, initials, hospital numbers, etc.) and confirm in their manuscript that consent to publish identifiable material was obtained in accordance with international and institutional ethics policies.
Special Issues Policy
The editorial board periodically announces Special Issues focusing on emerging themes in cybersecurity. Special Issues follow the same peer-review standards and submission process as regular issues. Calls for submissions and deadlines are published annually on the journal’s website.
Appointment of Guest Editors
Guest Editors for special issues of the Mesopotamian Journal of CyberSecurity (MJCS) are selected based on their academic expertise, editorial experience, and professional reputation in cybersecurity and related disciplines. Potential Guest Editors may be nominated by the journal’s editorial board, current editors, or via self-nomination. All nominations are reviewed by the editorial board and approved by the Editor-in-Chief.
Guest Editors are responsible for:
- Defining the theme and scope of the special issue.
- Drafting the call for papers and coordinating with the editorial office for announcements.
- Managing manuscript submissions and peer review.
- Ensuring scientific rigor, originality, and ethical compliance throughout the process.
- Making final recommendations on manuscript acceptance in consultation with the Editor-in-Chief.
Setup of Special Issues
To propose a special issue, a formal proposal must be submitted that includes:
- The theme and objectives of the special issue.
- The target audience and potential contributors.
- Names and affiliations of proposed Guest Editors.
- A clear timeline for submission, review, and publication.
Proposals are evaluated by the editorial board and approved by the Editor-in-Chief. Once approved, the Call for Papers (CFP) is announced and disseminated via the journal’s website, academic networks, and partner institutions. A defined timeline is established for:
- Manuscript submission and initial screening.
- Double-blind peer review.
- Revisions and final approval.
This ensures each special issue aligns with MJCS’s regular publication schedule and quality standards.
Editorial and Review Process
All manuscripts for special issues are submitted through the MJCS Online Submission System and undergo double-blind peer review, identical to standard issues. The process includes:
- Initial screening by Guest Editors to ensure scope and quality alignment.
- Double-blind peer review by qualified reviewers selected for subject expertise.
- Revision process guided by reviewer and editor feedback.
- Final approval by the Editor-in-Chief based on Guest Editors’ recommendations.
Accepted manuscripts are professionally edited, proofread, and published online as part of the special issue. Each special issue is promoted through MJCS’s official website, indexing databases, and academic networks, and performance metrics are tracked post-publication.
Guidelines and Review Process
All submissions to special issues are subject to the same editorial, ethical, and peer-review standards as regular issues of MJCS. Authors must follow the journal’s author guidelines and ethical policies in full. Each special issue is managed under the supervision of the Editor-in-Chief to ensure compliance with COPE standards.
Publication Timing
The Mesopotamian Journal of CyberSecurity (MJCS) publishes one continuous annual issue, with accepted papers released incrementally throughout the year. Special issues are scheduled and released as supplements to the annual volume upon completion of all peer-review and production stages.
Standards of Reporting
The Mesopotamian Journal of CyberSecurity (MJCS) promotes research transparency, reproducibility, and verification. Authors must communicate their research clearly and comprehensively, providing sufficient detail about the study rationale, design, data collection methods, analysis, and results to allow replication or verification by others. MJCS encourages adherence to established reporting standards and discipline-specific checklists (where applicable) to ensure high-quality scholarly communication.
Use of Third-Party Material
Authors are responsible for ensuring that any third-party material (e.g., text, figures, tables, images, datasets, video, music, screenshots, or other copyrighted content) included in their manuscript is used in accordance with applicable copyright laws and licensing terms.
- Short quotations or excerpts may be used for purposes of criticism, commentary, or review without formal permission, provided they are properly cited and fall under fair use or equivalent provisions.
- If authors wish to include any material not covered by fair use or for which they do not hold copyright, they must obtain written permission from the copyright owner prior to submission.
- All permissions must explicitly grant rights for online, open-access publication under the CC BY 4.0 license.
- When reusing material from other publications, authors must include full source citations and provide statements confirming that appropriate permissions were obtained.
The publisher and editorial board bear no responsibility for authors’ failure to secure permissions. Authors are fully liable for any infringement of third-party rights.
Use of Generative AI and AI-Assisted Technologies in Writing
AI Use by Authors
This policy refers solely to the use of AI tools in the writing process, not in the research itself (e.g., data analysis, simulation, or modeling).
Authors who use generative AI or AI-assisted technologies (e.g., ChatGPT, Gemini, Copilot, GrammarlyGO, etc.) in preparing their manuscripts must do so only to improve readability and language. These tools must not be used to generate scientific ideas, conclusions, or interpretations.
Author Responsibilities:
- The use of AI tools must always occur under direct human oversight and critical review.
- All content generated or modified with AI assistance must be checked for factual accuracy, originality, and bias by the authors.
- Authors are fully accountable for the final text and its integrity, regardless of AI involvement.
- Authors must include a disclosure statement specifying any AI-assisted tools used and their purpose (e.g., language editing). This statement will appear in the published article.
- AI tools cannot be credited as authors, since authorship requires human accountability, intellectual contribution, and the ability to respond to post-publication queries.
AI in Peer Review
The Mesopotamian Journal of CyberSecurity prohibits the use of generative AI tools (such as ChatGPT or similar) in the peer review process. Manuscripts are considered confidential documents, and uploading them to external AI systems violates author confidentiality and data protection principles.
Reviewers must not input any part of a submitted manuscript, review text, or reviewer comments into generative AI systems. The peer review process must rely solely on human judgment, expertise, and ethical responsibility.
MJCS supports the responsible development of AI technologies that respect confidentiality, privacy, and data protection, and will adapt its policies as industry standards evolve.